High seas cybersecurity alerts, risks rising in the global commercial shipping fleet
Maritime industry risk-management company updates ship owners and operators on current cybersecurity threats and weak links in ocean carrier company defences
In 20th-century wartime, the maritime security catchphrase was “loose lips sink ships”; in 21st-century cyber-wartime, it’s “cybersecurity slips sink ships.”
Well, maybe not sink, but those slips can seriously compromise multibillion-dollar ocean carrier operations and bottom lines.
DNV’s recent Onboard Cybersecurity: Key Insights and Best Practices event updated shippers on cybersecurity threats from inadequate cybersecurity defences.
First, the good news.
According to the maritime industry risk-management company’s survey of close to 500 maritime industry professionals from 50 countries, most shipping companies are now taking cybersecurity threats seriously.
Svante Einarsson, DNV Cyber’s head of maritime cybersecurity advisory, said almost three-quarters of survey respondents say they are spending more on cybersecurity than they did last year.
He added that the industry is confident “that we are doing quite well in terms of cybersecurity; 84% are saying that they have a good posture on dealing with it in their organization; 71% are thinking that they can come back to normal operation after a cyberattack [quickly].”
Einarsson conceded that he did not have a definition “of what quick is here, but still, quite high numbers from my point of view.”
And shippers need high cybersecurity awareness numbers because cyberattacks are multiplying.
According to DNV’s survey, 72% of respondents said their organization’s industrial assets are more vulnerable to cyberattacks than ever before.
The company’s Maritime Cyber Priority 2024-2025 report found that one in three (31%) maritime industry professionals surveyed said hackers had infiltrated their companies at least once in the 12 months leading up to October 2024. In DNV’s 2023 study, only 17% of survey respondents had suffered a serious cybersecurity breach during the previous five years.
CyberOwl CEO Daniel Ng has estimated that shipping companies will now, on average, experience between 65 and 80 cybersecurity incidents per year.
The DNV company monitors cyber-risks and threat management onboard commercial ships.
Maritime freight movement is a multibillion-dollar industry critical to the global economy. That makes it an attractive target for cyber-criminals and political activists.
It is also a complex supply chain whose patchwork of technological hardware and proprietary software and abundance of data access points and users increase its vulnerability to a wide range of security breaches that are difficult to police and plug.
Successful security breaches are expensive.
In June 2017, a cyberattack crippled the world’s largest maritime container shipping company’s booking system, stalled tracking of its containers and disrupted operations at its container terminals for approximately two weeks.
The financial cost to A.P. Møller-Mærsk (CPH:MAERSK-B) was estimated at US$300 million. The cost to its reputation is harder to quantify in dollars and cents, but by any measure, it was significant.
Since the 2017 Maersk attack, all four of the world’s largest container shipping companies have suffered at least one major cybersecurity breach.
During DNV’s July 2 Onboard Cybersecurity discussion, Ng provided examples of recent maritime cyberattacks.
One simultaneously disrupted the communications of 116 crude oil tankers belonging to two Iranian companies.
“By compromising a common vulnerability across the communication systems,” Ng said, “the hackers were able to shut down … the communication networks of all of the vessels across these two fleets in one go.”
He added that Lab Dookhtegan, an activist group with advanced, nation-state-level hacking capabilities, has taken credit for the attack ostensibly aimed at ships violating Iranian oil sanctions.
“… in the world of cybersecurity, if you’re able to find a common vulnerability, a common weak point, then unfortunately, an attack [can] affect multiple vessels at the same time”
– Daniel Ng, CEO, CyberOwl
Leaving aside the suspected motivation, Ng said the attack was concerning because most commercial shipping cyberattacks focus on a single vessel.
“But in the world of cybersecurity, if you’re able to find a common vulnerability, a common weak point, then unfortunately, an attack [can] affect multiple vessels at the same time.”
That is a problem because, as Ng pointed out, most shipping companies’ emergency response and crisis management systems focus on single-vessel attacks.
“So, it's time for us to elevate that into a fleetwide view.”
That sounds like an expensive elevation.
Had the Iranian oil tankers attack been an isolated incident, Ng said, the global shipping industry would be less concerned.
But Anonymous ensured it was not.
According to Ng’s second example, the notorious hacking group’s phishing operation breached a ship’s anti-malware defences. An email to head office from the ship’s concerned captain subsequently opened the door to onshore fleet operations for Anonymous.
Ng said the attack was the first his company had identified in which a ship had been targeted to access onshore office operations.
Normally, attackers seek access to ship operations through onshore office cybersecurity breaches.
Access to shipping office operations from a ship’s captain, Ng said, “clearly [has] a much wider set of implications.”
So, the hackers in this case exploited human [crew] error. That is a difficult window of opportunity for shipping companies to close.
Most employ thousands of people from a wide range of countries to crew their ships. That makes training and policing a ship’s crew more complicated than training and policing the smaller and more consistent number of head office staff.
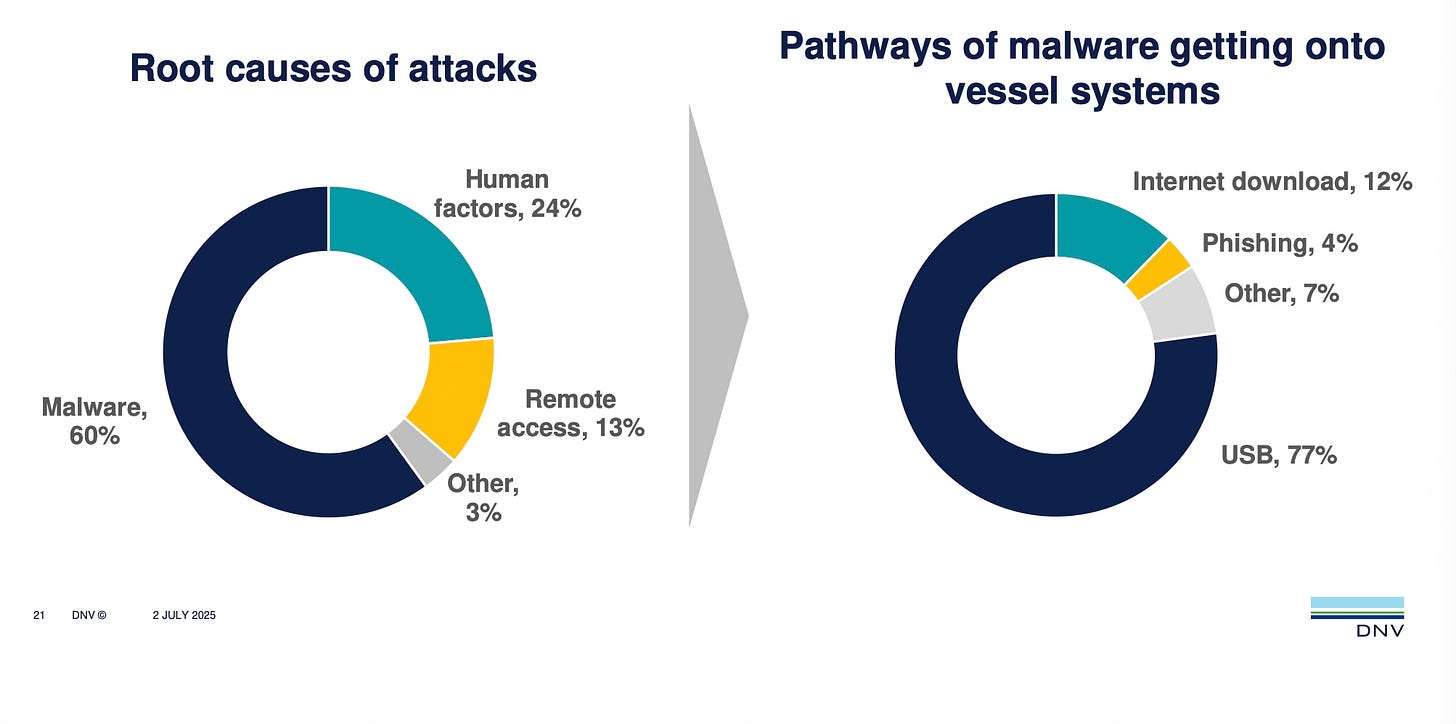
And human factors account for 24% of cyberattacks, but far more result from malware (60%), according to DNV data.
And USB thumb drives provide 77% of malware pathways into shipping systems.
So, cybersecurity awareness, rigorous crew training and consistent security system updates are fundamental to ocean carriers’ first line of defence in the 21st-century cybersecurity wars.
The challenge here is that awareness of cybersecurity vulnerabilities up and down a ship’s supply chain and chain of command is, for the most part, inadequate.
Also inadequate is cybersecurity awareness at the top of the ocean carrier food chain.
DNV’s report shows that only one in six ship owners understands what to expect of a new cyber-secure vessel.
Couple that lack of clarity with what Einarsson said are numerous indicators in DNV’s survey of commercial shipping’s false sense of cybersecurity, and you have fertile phishing grounds for cyber-crooks, hacker activists, ransomware gangs and the rest of the 21st-century’s online criminal underworld.
www.linkedin.com/in/timothyrenshaw
@trenshaw24.bsky.social
@timothyrenshaw